
Hidden threats are draining profit from complex operations.
Most organisations never see where it’s happening.
We help you find it - and stop it before it escalates.
You’ve built a complex operation.
Systems are connected. Suppliers are integrated. Processes are designed to move quickly and efficiently.
At that level, a degree of loss is often accepted. It’s written off as delay, error, or the cost of doing business.
But not all loss is operational.
In many organisations, a proportion of that loss is driven by theft, fraud, or coordinated activity moving quietly through the business.
The problem is not that it’s invisible.
It’s that it blends in.

The gap
Most organisations are not underinvesting in security.
They are investing heavily in tools, compliance, and oversight.
The issue is where that investment is focused.
Real exposure often sits elsewhere - in operational processes, supplier relationships, system interdependencies, and trusted access.
This creates a gap between what feels protected and what actually is.
That gap is where loss occurs.
What’s actually happening
Modern threats don’t arrive as obvious incidents.
They develop over time.
They move through systems, suppliers, and people who already have access. They observe, test, and adapt.
In many cases, they operate undetected for months before any action is taken.
By the time it becomes visible, the damage is already done.
At the same time, organisations continue to optimise for performance.
Processes become faster. Systems become more connected.
Without the right perspective, those improvements can increase exposure rather than reduce it.
The missing piece
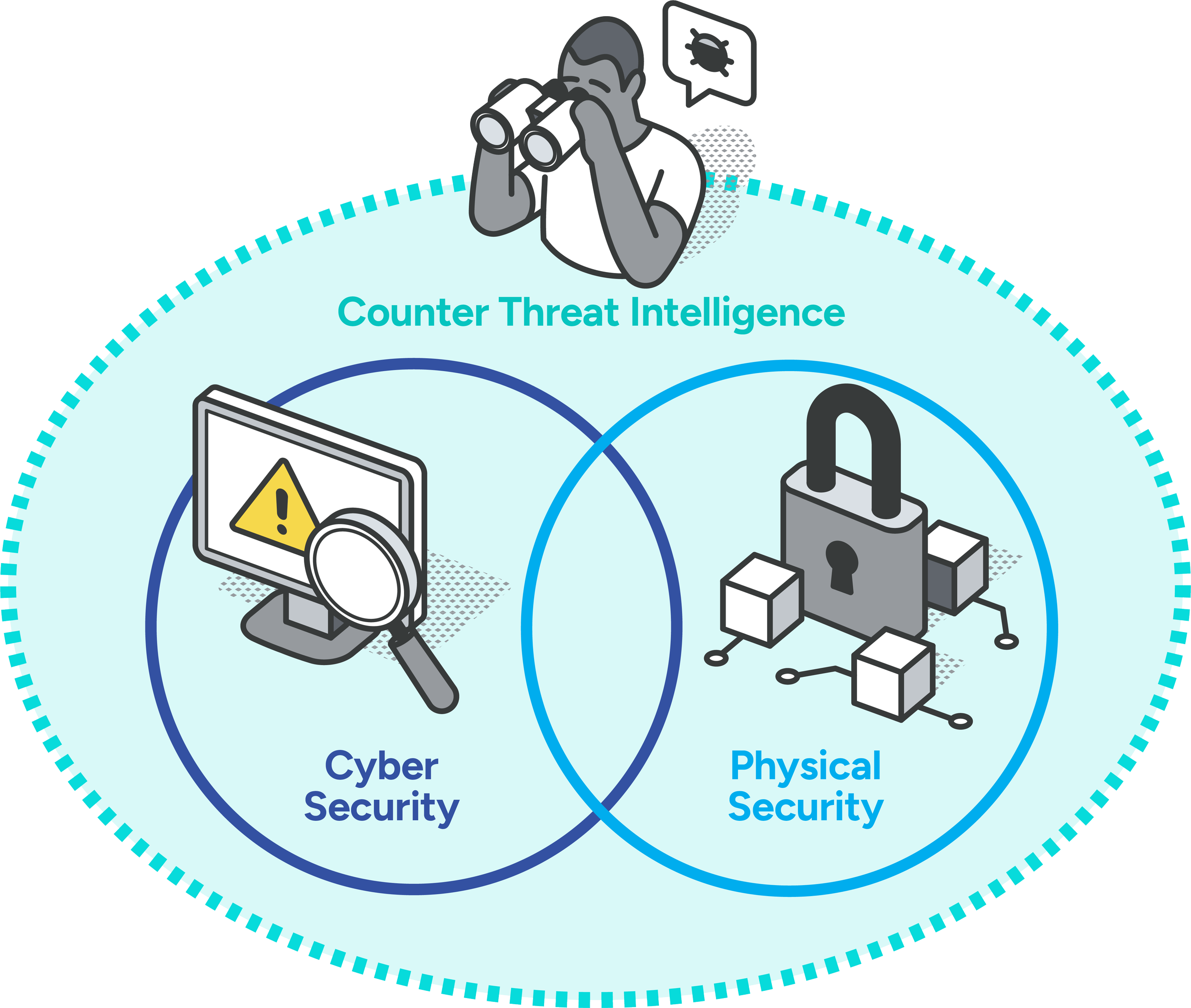
Most organisations already have two forms of protection in place.
Cyber Security - Protecting systems, data, and networks.
Physical Security - Controlling access, environments, and assets.
These are essential. And in most cases, they are already being handled well.
But there is a third element that is almost always missing.
The 3 pillars of security
Government and military environments don’t rely on two layers of protection.
They operate with three.
1) Cyber security
2) Physical security
3) Counter threat intelligence
The first two protect what you have.
The third focuses on who is targeting you, how they operate, and what they are likely to do next.
What Five Eyes does
Five Eyes provides intelligence-led security that helps you understand where your business is genuinely exposed.
We work across operations, cyber, physical security, and supply chain to identify:
Where loss is actually occurring
What is inefficiency and what is not
How threats are developing within your environment
Where systems, suppliers, or people create vulnerability
What to change to reduce risk immediately
We don’t replace your existing teams or partners.
We work alongside them to bring clarity, alignment, and focus where it’s missing.
Why we’re different
Our team comes from environments where the threat is real and the margin for error is minimal.
That includes former FBI cyber operations, British military intelligence, and specialist operators who have worked in high-consequence environments.
We understand how adversaries think, how systems are exploited, and how vulnerabilities are used in practice.
This is not theoretical security.
It is applied experience, transferred into commercial organisations.

How we can help
When you can clearly see where loss and exposure exist, decisions become simpler.
You stop chasing the wrong problems.
You stop writing off what could be prevented.
You align investment with actual risk.
The result is:
Reduced loss
Stronger operational control
Clearer visibility of risk
Better decision-making at leadership level
Greater confidence in how your business is protected
Some problems don’t look like problems - until you know where to look.
If you’re responsible for performance, risk, or operations, it’s worth understanding what’s really happening beneath the surface.
